Darkweb Threats
- Gathering place for cybercriminals.
- Visiting Dark web are not lawful in themselves.
- You could stumble on illegal activity without even realizing it.
- Cybercriminals can inevitably abuse the power associated with dark web.
Most Attacks are Planned and Facilitated from Darkweb

Threat Objects and Sources
- Specific sources are established by malicious actors
- These sources are targeted against your company
- They cause brand damage to your organization
- They are also used for launching attacks

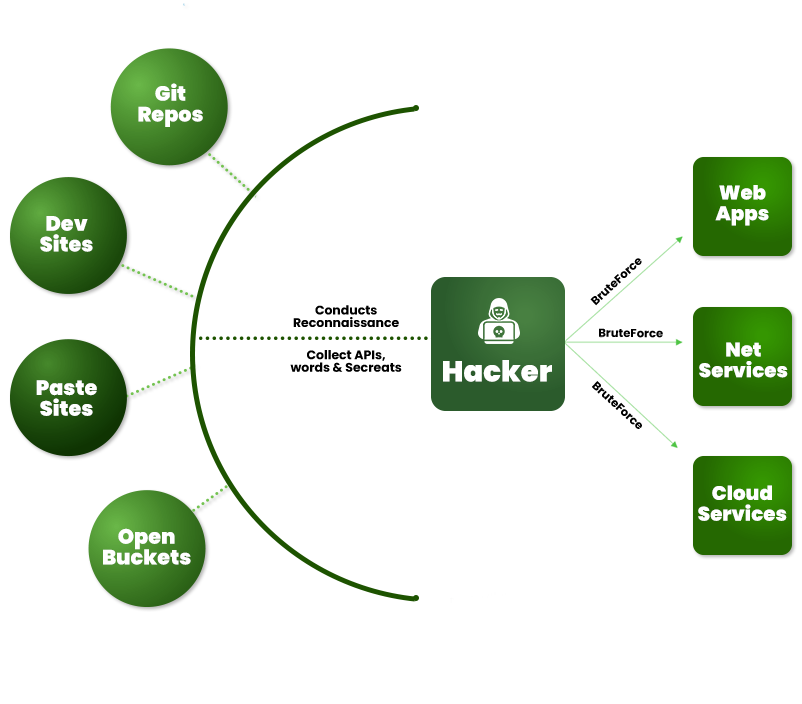
Your Data Weaponized
Hackers usually find
large number of API Keys,
Credentials on GitHub
Developers use paste sites
for collaboration, and
leave sensitive info there
Forums which are used
for discussion on code, also
have a lot of sensitive info
Explore Threat Intelligence Services
Explore focused threat intelligence services designed to help your organization monitor dark web exposure, identify external attack surface risks, detect brand abuse, and coordinate takedown actions against malicious or impersonating assets.
Darkweb Intelligence 24/7
Continuously monitor dark web sources, underground forums, leaked credential references, exposed data mentions, and attacker activity linked to your organization.
Attack Surface Monitoring
Identify, map, and monitor internet-facing assets, exposed services, misconfigurations, shadow IT, and external risks that increase organizational attack surface exposure.
Brand Monitoring Service
Track fake domains, phishing pages, impersonation attempts, fraudulent profiles, logo misuse, and suspicious brand references across external channels.
Take Down Services
Support evidence collection, validation, abuse reporting, escalation, and takedown coordination for phishing pages, fake domains, impersonation assets, and malicious online content.
Get started today!
To know more and to setup an experiential demo
