Security Testing
- Identify vulnerabilities across infrastructure, applications, cloud and exposed assets.
- Move beyond one-time testing with cycle-based, periodic and continuous models.
- Track vulnerability lifecycle from detection to remediation and closure.
- Build audit-ready visibility with automation, SLA tracking and risk reporting.
Point-in-Time Testing Does Not Match Modern Risk
- New assets and exposed services can appear after every testing cycle.
- Code changes and configuration drift silently introduce fresh security gaps.
- Open findings remain unresolved without ownership, SLA tracking and retesting.
- Raw scanner noise creates confusion instead of clear remediation priorities.

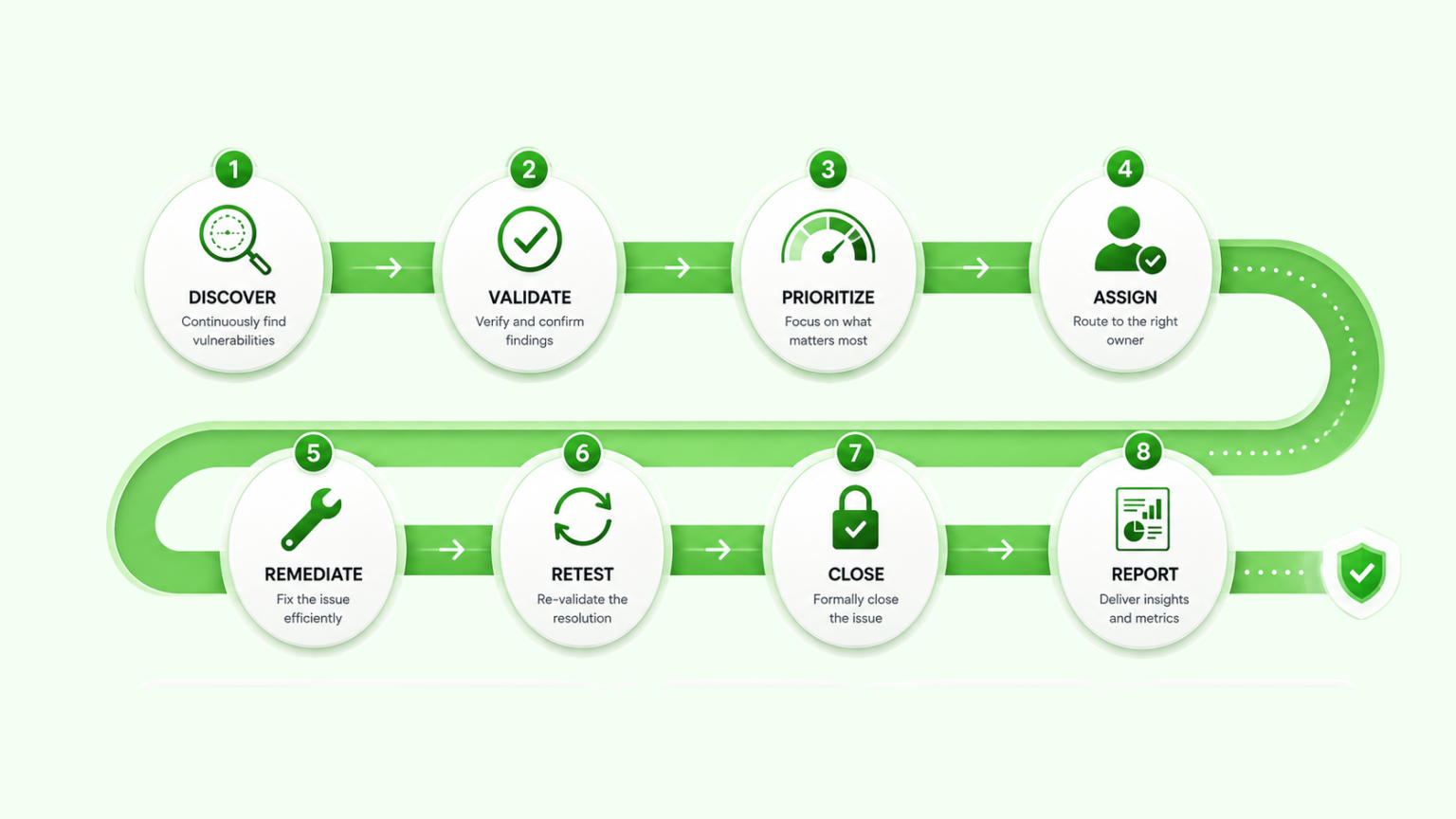
From Security Findings to Lifecycle Closure
Security Testing Engagement Models

Cycle-Based Testing
A structured security assessment performed for a defined scope, project, compliance cycle or annual testing requirement.
- Annual or half-yearly VAPT
- Project-based security assessment
- Infrastructure, application or cloud scope
- Compliance and audit-driven testing

Periodic Security Testing
Recurring testing performed at an agreed frequency to validate changing assets, releases, patches and security posture.
- Monthly or quarterly testing cycles
- Patch and remediation validation
- Testing after major changes
- Better visibility for dynamic environments

Continuous Vulnerability Management
An ongoing model focused on faster detection, ownership assignment, SLA tracking, retesting and vulnerability closure.
- Continuous vulnerability detection
- Asset owner and SLA tracking
- Remediation follow-up and retesting
- Lifecycle visibility until closure
Explore Security Testing Services
Explore Castellum’s security testing services across vulnerability assessment, application security, automation-driven vulnerability management, and configuration control validation.
VAPT & Vulnerability Management
Identify, validate and manage vulnerabilities across infrastructure, applications, cloud and exposed assets through structured testing and lifecycle tracking.
Application Security Testing & Audit
Assess application risk across design, code, dependencies and runtime behavior using black-box, grey-box, secure code review and threat modeling approaches.
Vulnerability Management Automation
Automate scan scheduling, event-based detection, deduplication, dashboarding, remediation tracking and CVE intelligence enrichment.
Configuration & Control Automation
Automate configuration checks, control extraction, benchmark mapping and audit-ready reporting across infrastructure, cloud, IAM and security platforms.
Get started today!
To know more and to setup an experiential demo
