SECURITY TESTING SERVICES
Vulnerability Management Automation
- Automated scanner scheduling and execution.
- Event-driven vulnerability detection for changing environments.
- Deduplicated findings with dashboard-driven visibility.
- Remediation workflow, SLA tracking and CVE intelligence enrichment.
Designed for Automated Vulnerability Operations
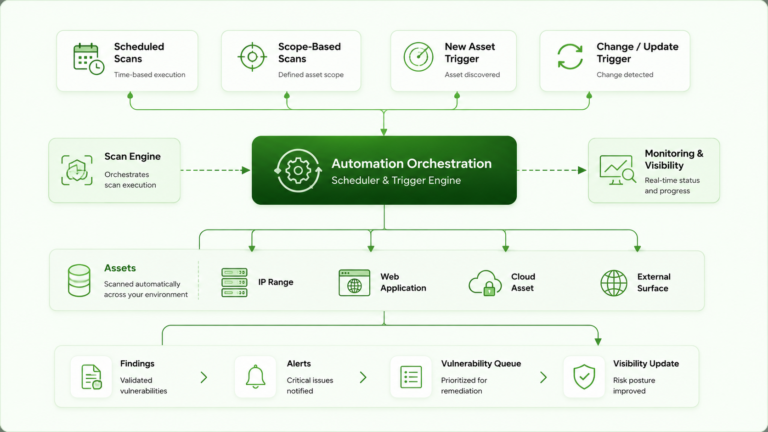
Automated Scan Scheduling
Run vulnerability scans on defined schedules, approved scopes or change-driven triggers across infrastructure, applications, cloud and exposed assets.
Automated Scan Scheduling
Run vulnerability scans on defined schedules, approved scopes or change-driven triggers across infrastructure, applications, cloud and exposed assets.
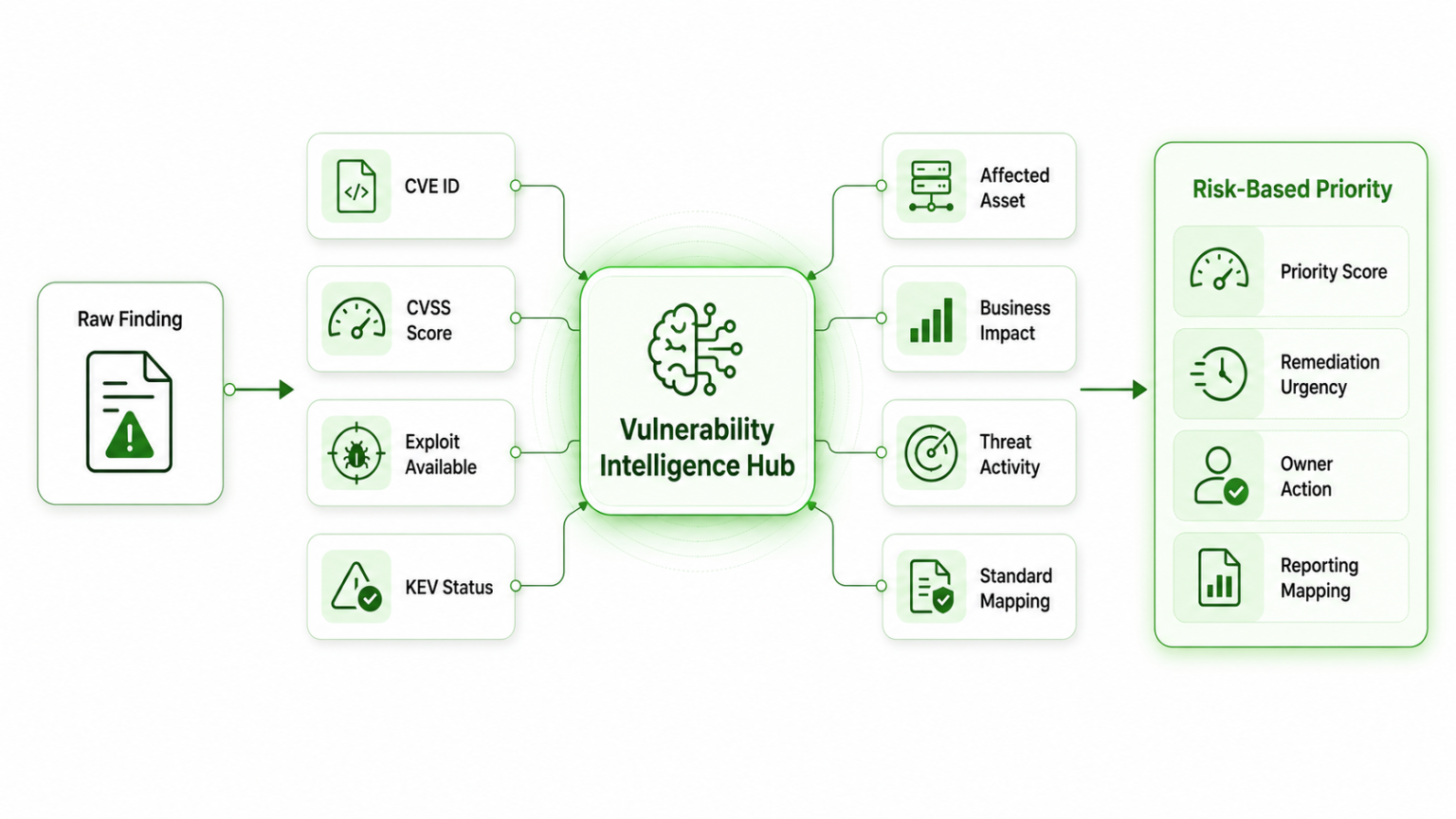
Risk-Based Prioritization
Prioritize vulnerabilities using severity, exploitability, CVE context, asset exposure and business impact instead of relying only on scanner scores.
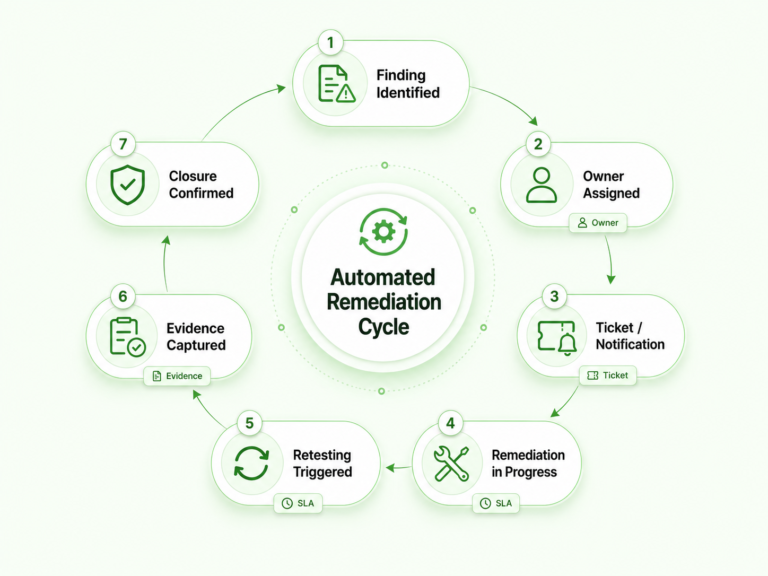
Remediation & Closure Tracking
Track ownership, SLA timelines, remediation progress, retesting status and closure evidence from one operational vulnerability view.
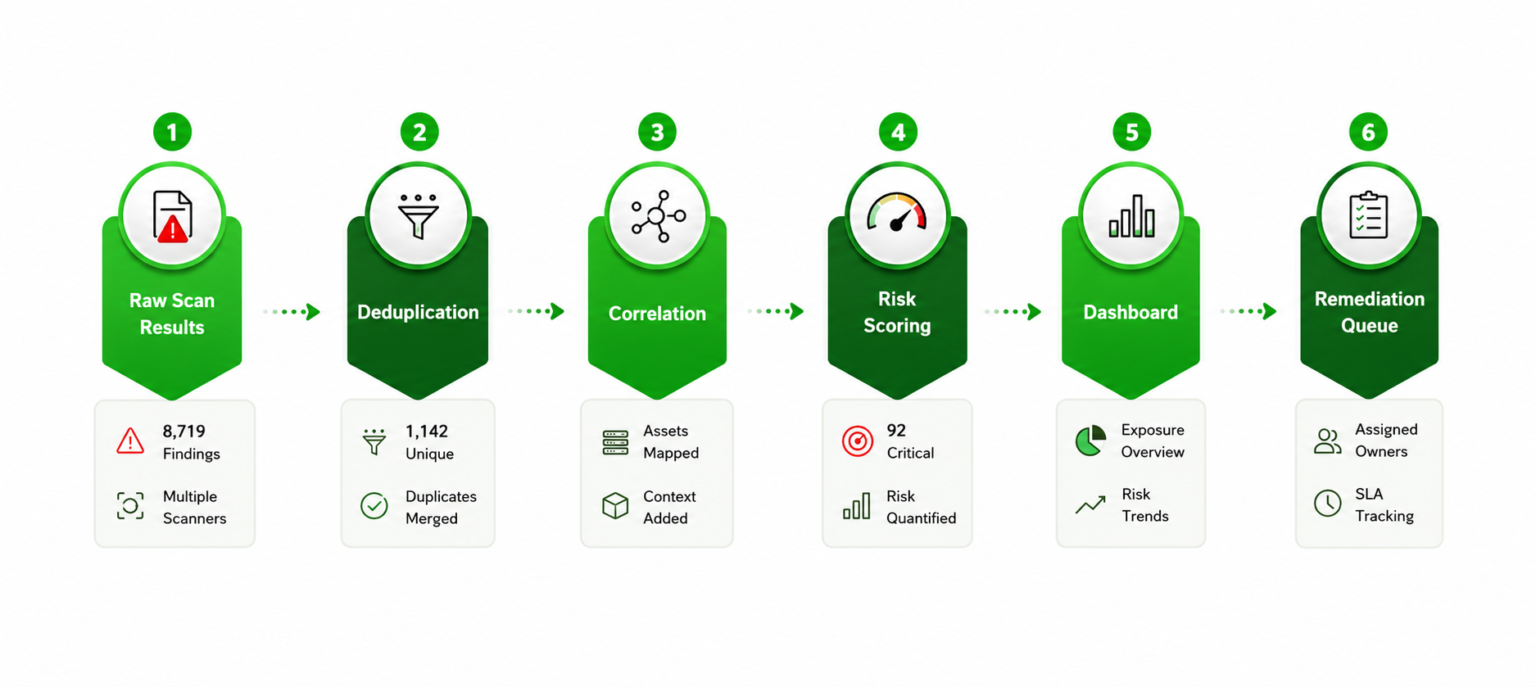
Deduplication and Prioritization
Remediation Workflow Automation
Enrich Vulnerabilities With CVE and Threat Intelligence Context
Ready to Automate Vulnerability Operations?
To know more and to setup an experiential demo